Cyber insurance in the UK typically covers financial losses from ransomware, data breaches, business interruption, and third-party claims. Modern mid-market policies include first-party losses (data recovery, business interruption, ransomware extortion), third-party liability (regulatory defence, customer claims), and incident response services. Common exclusions include war and state-sponsored attacks (Lloyd's 2023 mandate), known unpatched vulnerabilities, and social engineering without a specific endorsement.
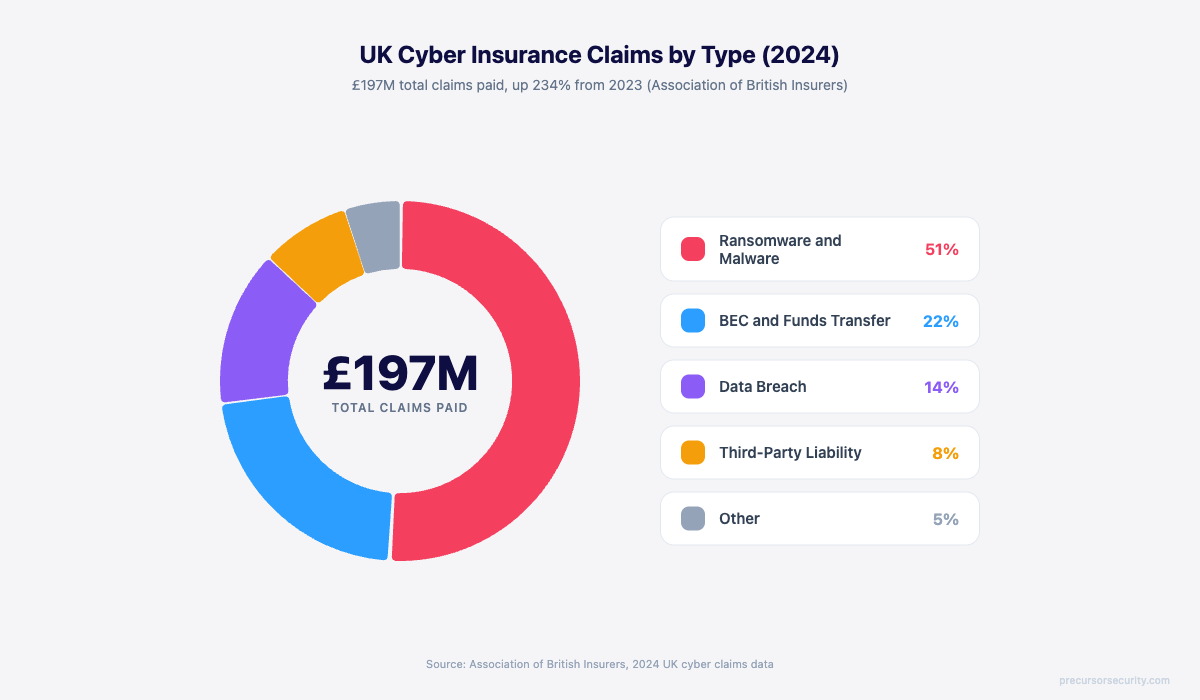
UK businesses paid out £197M in cyber insurance claims in 2024, a 230 percent increase on the previous year. Premiums followed. The market is now £1.56B and growing at 13 percent annually, but the cover behind those premiums has changed structurally. What a UK mid-market policy paid for in 2020 is not what one pays for in 2026, and the exclusions that catch buyers out at claim time have multiplied.
This guide breaks down what cyber insurance actually covers, which exclusions matter most, and what to check before signing a policy or accepting a renewal quote. The goal is honest clarity, not a sales pitch.
What is cyber insurance, and who buys it in the UK?
Cyber insurance is a commercial insurance product that covers financial losses arising from cyber incidents: ransomware, data breaches, denial of service attacks, regulatory action following a breach, and third-party claims from customers or partners harmed by a security failure.
The UK cyber insurance market reached £1.56B in 2024 and is growing at 13.18 percent compound annually, on track to reach £3.08B by 2031. Buyers fall into three groups:
- SMEs (10 to 250 employees) typically buy £1M to £5M of cover, often triggered by a supplier security questionnaire or a Cyber Essentials certification cycle. Annual premiums range from £350 for microbusiness cover to £5,000 for a typical 100-employee firm.
- Mid-market organisations (250 to 2,500 employees) buy £5M to £25M of cover, with annual premiums of £8,000 to £50,000. The buying decision usually involves a CFO, CISO or IT Director, and a Risk Manager.
- Enterprise (2,500 plus) buy bespoke policies with limits in the hundreds of millions, layered across multiple insurers.
Every modern UK cyber policy bundles two halves: first-party losses (the costs the insured suffers directly) and third-party liability (claims brought against the insured by others). The terms "cyber insurance" and "cyber liability insurance" are used interchangeably in UK policy wording, though strictly speaking "cyber liability" refers to the third-party half.
What does cyber insurance actually cover?
A standard UK mid-market cyber policy covers nine categories of loss, divided into first-party, third-party, and incident response services. The exact wording varies by carrier, but the structure is consistent.
The table below summarises the nine coverage sections, typical UK mid-market sub-limits, and the most common exclusion or carve-out for each.
| Coverage section | What it pays for | Typical UK mid-market limit | Common exclusion or carve-out |
|---|---|---|---|
| Business interruption | Lost revenue and increased operating costs during a cyber-caused outage | Full policy limit, 12-month indemnity period | Outages caused by upstream provider failure |
| Data recovery | Cost of restoring corrupted, encrypted, or lost data | Full policy limit | Backup data that was never created |
| Cyber extortion | Ransomware payments, negotiation, decryption tools | Sub-limit (often 50 percent of policy limit) | State-backed actors (Lloyd's 2023 mandate) |
| System rectification | Cost of restoring compromised systems to known-good state | Full policy limit | Replacement of physical hardware (bricking) |
| Crisis management | PR, customer notification, credit monitoring | Sub-limit £100k to £500k typical | Reputation harm beyond defined scope |
| Privacy liability | Customer claims from data breach | Full policy limit | Acts predating policy inception |
| Regulatory defence | Legal costs defending against ICO, FCA, or other regulator | Sub-limit £250k to £2M | Fines themselves where not insurable by law |
| Media liability | Defamation, IP, copyright via digital channels | Sub-limit | Wilful or intentional acts |
| Cyber theft and social engineering | Funds transfer fraud caused by impersonation | Often endorsement, not base cover | BEC without specific endorsement |
The right way to read a quote is column by column. The coverage section tells you what the insurer pays for, the sub-limit tells you the actual ceiling on that section (which is usually lower than the policy headline), and the exclusion tells you which scenarios the section will not respond to. The combination of these three is what determines whether a future claim gets paid or denied.
What first-party losses does cyber insurance cover?
First-party losses are the costs the insured suffers directly as a result of a cyber event. These are the line items that hit the P&L when an incident lands.
Business interruption is usually the largest single first-party category. A ransomware event that takes operations offline for two weeks can cost a £50M revenue mid-market firm anywhere from £400k to £2M in lost margin alone, before accounting for staff overtime, supplier penalties, and customer recovery costs. The insurance pays these losses for the duration of the indemnity period, usually 12 months from incident date.
Data recovery covers the cost of restoring lost or corrupted data. The cost depends entirely on what backups exist and whether they have been tested. Organisations with 3-2-1 backup architectures and recent restore tests recover in days at low cost. Organisations whose backups were connected to the same network the ransomware encrypted recover in weeks or months at significant cost. Data shows median ransomware claim severity is £2.4M for organisations running basic antivirus, falling to £60k for organisations running managed detection and response with isolated backups.
Cyber extortion pays for ransomware payments, negotiation services, and decryption tools where the insurer's panel team approves the payment. UK insurers typically apply a sub-limit (often 50 percent of the headline policy limit) on ransomware cover and require pre-approval from their incident response team before a payment is authorised. Following the Lloyd's 2023 mandate, state-backed ransomware actors are excluded from Lloyd's-placed policies entirely, which causes attribution disputes when the actor is unclear.
System rectification pays for restoring compromised systems to a known-good state. This includes forensic investigation, system rebuild, and the labour cost of returning the environment to operational status.
Crisis management is the bundled service category most buyers undervalue. It pays for the PR firm, customer notification, and credit monitoring services that turn a quiet incident into a managed communications exercise rather than a public reputation event.
What third-party liability does cyber insurance cover?
Third-party liability is what the insurer pays when others bring claims against the insured.
Privacy liability is the most-claimed category. Customers whose personal data was compromised in a breach can bring civil claims under UK GDPR. The insurer covers legal defence and any settlement up to the third-party limit. Class actions are increasingly common in the UK following high-profile breaches.
Regulatory defence covers the legal costs of defending against ICO, FCA, or other regulator action following a breach. The 2018 introduction of UK GDPR raised the maximum ICO fine to £17.5M or 4 percent of global turnover, whichever is higher. Most UK cyber policies cap regulatory defence cover at £250k to £2M, well below the maximum exposure. UK GDPR fines themselves are sometimes uninsurable under English public-policy doctrine, depending on whether the breach was reckless or merely negligent. Read the policy wording carefully on this point.
Network security liability pays for third-party claims arising from a security failure that harmed others. This includes supply chain spillover (your compromise causes a customer's compromise), denial of service attacks launched from the insured's infrastructure, and contractual indemnities owed to clients.
Payment card industry liability is a niche sub-category that pays PCI DSS fines and assessments where card data was compromised. Relevant only for organisations that handle card data directly.
What incident response services are included in a cyber policy?
This is the most undervalued part of cyber insurance. Modern policies bundle a panel of incident response services that activate immediately on notification, often before any settlement question is even discussed.
A typical UK mid-market policy includes:
- 24/7 incident response hotline answered by the insurer's panel IR firm
- Forensic investigation by accredited firms (often DFIR specialists)
- Legal counsel familiar with breach notification, regulatory liaison, and contractual obligations
- PR and crisis communications support during and after the incident
- Ransomware negotiation services where applicable, including verification of decryption tool functionality
- Customer notification and call centre support for breach notification at scale
- Credit monitoring services for affected individuals where required by law
The hidden value is that these services are pre-vetted, pre-contracted, and immediately available. An organisation without a cyber policy that suffers an incident has to find, contract, and onboard each of these services under crisis conditions. The first 72 hours of an incident are usually where the difference between a contained event and a public crisis is made. Having the IR panel activated within minutes of notification is, in many cases, more valuable than the financial cover itself.
For organisations buying incident response retainer services directly, the cyber policy and the retainer are complementary. The retainer ensures a known team is on call. The policy ensures the financial cost is covered.
What does cyber insurance not cover? (The exclusions that catch buyers out)
This section is the one most buyers skip and then regret reading at claim time. Modern UK cyber policies include 12 to 15 distinct exclusion categories. They fall into three groups: structural exclusions that cannot be removed, exclusions negotiable via endorsement, and exclusions that can be closed by demonstrating control evidence.
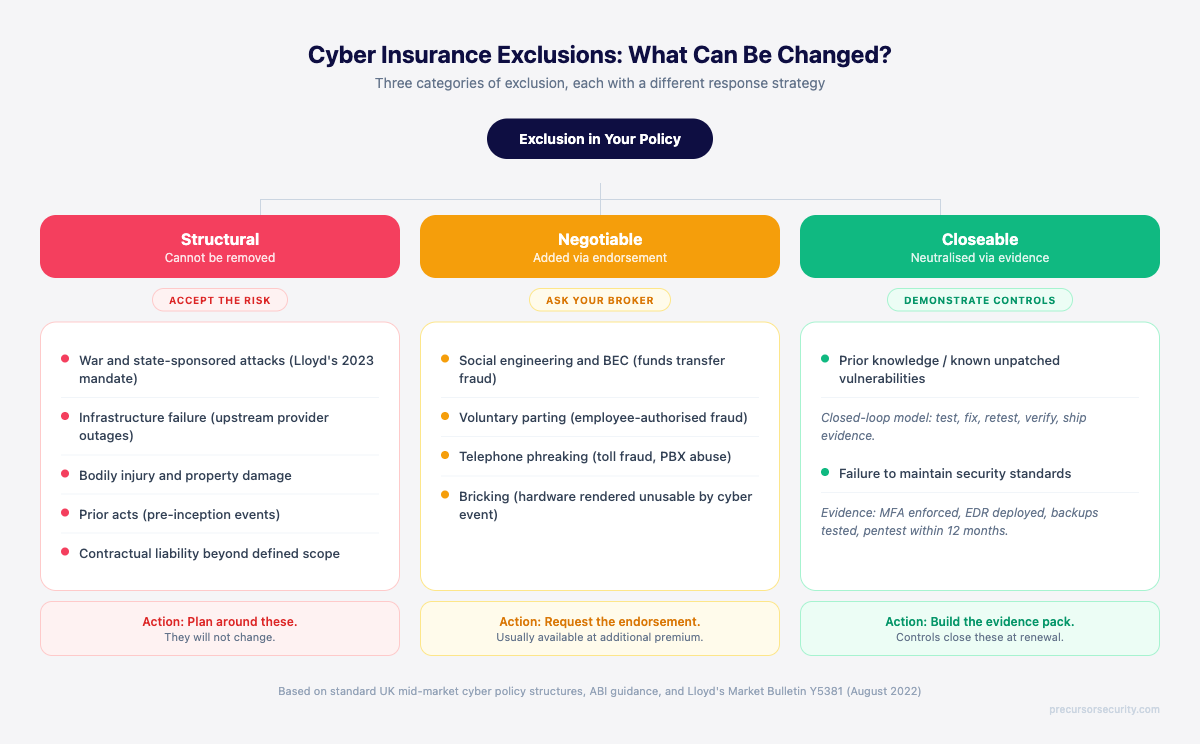
Structural exclusions
War and state-sponsored cyber attacks. In March 2023, Lloyd's of London issued Market Bulletin Y5381 mandating that all Lloyd's-placed cyber policies exclude state-backed cyber operations. The mandate uses model clauses LMA5564 through LMA5567. State attribution disputes are now one of the largest sources of claim friction. NotPetya was the precedent: insurers initially declined claims by attributing the attack to Russian state actors, leading to multi-year legal disputes. The mandate now codifies that exclusion across the entire Lloyd's market.
Infrastructure failure. Outages caused by upstream providers (power, telecoms, cloud, ISP) are typically excluded. The reasoning is that these are insured separately under business interruption or technology errors and omissions cover.
Bodily injury and property damage. Cyber policies cover digital and financial loss only. Physical consequences (a hospital patient harmed by a ransomware-caused medical device failure, for example) require general liability or product liability cover.
Prior acts. Events that occurred before the policy inception date are excluded entirely. Buyers switching insurers should check whether the new policy includes a retroactive date that protects against acts before the new cover started.
Exclusions negotiable via endorsement
Social engineering and business email compromise (BEC). Most base UK cyber policies exclude funds transfer fraud caused by social engineering, where an employee was deceived into authorising a payment. A specific "social engineering" or "fraudulent instruction" endorsement adds the cover back, usually at additional premium. BEC is now among the most frequent claim types in the UK mid-market. If your finance team handles supplier payments, this endorsement is essential.
Telephone phreaking. Toll fraud and PBX abuse are sometimes base cover, sometimes endorsement. Worth checking explicitly.
Bricking. The cost of replacing physical hardware rendered unusable by a cyber event (the literal "bricking" of a device beyond software recovery) is sometimes excluded from base cover and added by endorsement.
Exclusions closeable via control evidence
Prior knowledge / known unpatched vulnerabilities. The most contentious exclusion in UK cyber insurance. The clause voids claims where the insured "knew or ought to have known" about a vulnerability and failed to remediate it. A penetration test report identifying risks that were never closed creates documented prior knowledge. Closed-loop remediation, where findings are tested, fixed, retested, and verified before the evidence pack ships, neutralises this trap. Where a finding remains genuinely open at renewal, it is disclosed explicitly so the broker can negotiate a time-bound carve-in or sublimit. Surprise at claim time is what the closed-loop model is designed to prevent.
Failure to maintain security standards. Many policies require specific controls (MFA, EDR, tested backups, recent penetration testing) as conditions of cover. Breach of warranty, where a control was supposed to be in place but was not, can void a claim entirely. The supplemental answers form the warranty. This is why misrepresentation matters so much: an optimistic application answer becomes a binding warranty and a route to denial.
How does a cyber insurance claim actually work?
The claims process moves through five stages: notification, triage, investigation, remediation, and settlement.
Notification. UK policies typically require notification within 48 to 72 hours of the insured becoming aware of an incident. Late notification is one of the most common reasons for claim denial. The clock starts the moment any individual at the insured organisation becomes aware that an incident may have occurred, not the moment the incident is confirmed.
Triage. The insurer's incident response panel team is activated. They scope the incident, deploy forensic resources, and engage legal counsel.
Investigation. The forensic firm produces a report establishing the initial access vector, the scope of compromise, the data accessed or exfiltrated, and the timeline of events. This report is the central document for everything that follows.
Remediation. Systems are restored, controls are reset, the environment is hardened to prevent recurrence. The insurer's panel handles or coordinates this work.
Settlement. The insurer reviews the forensic report, the policy wording, the supplemental answers (which are binding warranties), and any exclusions that may apply. The settlement is calculated and paid, usually in tranches as costs are incurred.
In 2024 to 2025, more than 40 percent of UK cyber insurance claims were rejected at some stage in this process. The most common reason is insufficient evidence that security controls were active at the time of breach, where the supplemental answers said one thing and the forensic report said another. The second most common reason is late notification.
What changed in cyber insurance in 2026?
Three things matter for 2026 buyers:
Premiums normalised after the 2021 to 2023 spike. Premiums climbed 50 to 100 percent across the UK mid-market between 2021 and 2023. They softened slightly in 2025 but underwriters tightened criteria in parallel. The result is that mid-market organisations with strong controls are paying less than they did at the 2023 peak, while organisations with weak controls are still paying premium increases or being declined entirely.
Underwriting moved from questionnaire to evidence-based. UK underwriters now verify application answers against external data (Shodan, DMARC records, dark-web credential monitoring, attack surface scans) before binding cover. The supplemental is no longer a self-declaration. It is a contractual representation that will be cross-checked.
Discounts became mechanical. WTW's 2025 UK cyber market update reports premium reductions of 10 to 40 percent for organisations with documented CREST-accredited testing and proactive control evidence. Beazley publishes an explicit optional controls programme offering up to 20 percent discount for buyers with external vulnerability assessment and documented IR plans. The discounts are no longer negotiated, they are calculated against a published rate card.
For organisations preparing for renewal, the Cyber Insurance Readiness programme maps each underwriter requirement to a specific evidence artefact. The pillar walks through the full process.
What should you check before signing a cyber insurance policy?
Eight things to check on any cyber insurance quote, in order:
- Headline policy limit and the sub-limits per coverage section. The headline limit is rarely the maximum payout for any single category. Ransomware, regulatory defence, and crisis management almost always carry separate sub-limits.
- Exclusion register. Read every exclusion in full. Identify which are structural, which are negotiable via endorsement, and which are control-evidence-closeable. Negotiate the negotiable ones.
- Retention (excess) per claim. Higher retentions reduce premium but transfer first-£X of every claim to the insured. £25k to £100k retentions are typical for mid-market.
- Notification window. Most policies require 48 to 72 hour notification. Some require 24 hours. The shorter the window, the higher the risk of inadvertent breach of policy condition.
- Warranties and conditions precedent. Anything the policy requires you to have in place (MFA, EDR, backups, recent penetration test, IR plan) is a warranty. Breach voids the claim.
- Incident response panel. Which forensic firms, legal counsel, and PR support are on the insurer's panel? Are they UK-based? Can you bring your own panel?
- Indemnity period for business interruption. 12 months is standard. Some policies offer 18 or 24 months for additional premium. Check whether your industry's typical recovery timeline fits.
- Renewal clause. Some policies have automatic renewal at the carrier's discretion. Some require active renewal each year. Understand which applies before signing.
For UK SMEs under £20M turnover, there is a cheaper starting point. Cyber Essentials Plus certification unlocks free £25,000 cover via IASME partner schemes. It is not a full mid-market policy, but it satisfies most supplier security questionnaires and is the most cost-effective baseline available in the UK market.
Frequently asked questions
What does cyber insurance not cover? Common exclusions include war and state-sponsored attacks (Lloyd's 2023 mandate, applies to all Lloyd's-placed policies), known unpatched vulnerabilities (the prior knowledge clause), social engineering and BEC unless specifically endorsed, infrastructure failures, contractual liability beyond defined scope, regulatory fines not insurable by law, and prior acts predating policy inception.
Is cyber insurance worth it for UK businesses? For UK organisations with revenue dependency on digital systems, cyber insurance covers the residual risk after security controls. UK mid-market premiums range from £3,000 for small businesses to £50,000 for organisations with complex environments. Many supplier contracts now require cover as a precondition of engagement. The choice is not between insurance and security controls. The choice is whether to transfer the residual risk after controls are in place. Without controls, premiums become uneconomic. With controls, evidence-based discounting (10 to 40 percent per WTW 2025) makes cover affordable.
What is the difference between cyber insurance and cyber liability insurance? The terms are used interchangeably in UK policy wording. Cyber liability insurance technically refers to third-party coverage (claims brought by customers, partners, or regulators). Cyber insurance covers both first-party losses (your costs) and third-party liability. In practice, all modern UK policies bundle both. When comparing quotes, compare coverage sections (ransomware, BI, liability, crisis response) rather than the label.
Does cyber insurance cover ransomware payments? Most UK cyber policies include ransomware extortion cover, subject to a sub-limit (often 50 percent of the headline policy limit) and pre-approval from the insurer's incident response team. Lloyd's-placed policies exclude state-backed ransomware actors per the 2023 mandate. UK government guidance discourages payment of ransoms, but does not prohibit it for private sector organisations outside specific sanctions contexts.
How much cyber insurance does a UK mid-market business need? Limits depend on revenue, sector, contractual obligations, and the data types processed. £1M to £5M is typical for UK SMEs. Mid-market organisations carrying sensitive data or operating in regulated sectors typically buy £5M to £25M of cover. The right way to size cover is to model the worst-case scenario for your specific business: how much business interruption would a 14-day outage cost, what regulatory exposure exists, what contractual indemnities are in place, and what would a major customer breach claim look like. That total is the floor for your headline limit.
Precursor Security is a CREST-accredited provider of penetration testing, social engineering testing, and security operations services based in Leeds, UK. Precursor's Cyber Insurance Readiness programme helps UK organisations close the supplemental gaps and unlock evidence-based premium discounts.
