Communicating Cyber Security Risk to the Board
You have fifteen minutes in front of the board. The previous agenda item ran over. One director is checking their phone. How you communicate cyber risk in the next quarter of an hour will determine whether the board leaves the room with confidence or concern - and whether you walk away with the support you need.
Communicating cyber security risk to the board means translating technical exposure into the language of governance: risk, cost, and business impact. A CISO (Chief Information Security Officer)'s job in the boardroom is not to explain how controls work, but to give directors the information they need to fulfil their oversight responsibilities and make informed decisions about risk appetite.
The DSIT Cyber Security Breaches Survey 2024 found that only 30% of UK businesses have a board member explicitly responsible for cyber security as part of their role, and just 75% rate it as a high priority for senior management - figures that drop sharply for smaller organisations. That gap between where cyber risk sits and how well it is governed falls squarely on the person standing at the front of the room.
To help address this, we have collated ten principles you can use to get your messages across effectively.
Why Should You Understand Your Role Before a Board Presentation?
When you are in the throes of the meeting and fielding difficult questions, it is easy to forget why you are there. The unconscious assumption is that you are there to make you and your team look good and defend your position. Remember why you are there: to help directors fulfil their governance obligations. You need to tell them what they need to hear, not what you want them to hear.
The UK Corporate Governance Code 2024 - published by the Financial Reporting Council (FRC) in January 2024 and now in effect for financial years beginning on or after 1 January 2025 - requires listed company boards to declare on the effectiveness of their material internal controls under Provision 29. For the vast majority of organisations, cyber security is a material operational risk that falls squarely within that obligation. Boards are not assessing your performance as a security professional. They are trying to fulfil a governance function, and a communication failure on your part does not just leave them uninformed - in our experience working with senior security leaders, a common outcome of communication breakdown is that boards form the impression that risk is not being managed.
For organisations in UK financial services, the obligation is more explicit still. The FCA's Operational Resilience Policy Statement PS21/3 requires boards to approve important business services and impact tolerances, with cyber attacks explicitly named as a primary resilience scenario. The March 2025 compliance deadline has now passed, meaning this is a present obligation, not a future consideration. Board-level security reporting is not optional for regulated firms - it is part of the regulatory architecture.
Why Does Having a Clear Objective Matter in Board Meetings?
A clear meeting objective shapes every slide and metric you choose. By having that clear objective in your mind, you can keep the conversation guided. This is no different - part of your preparation should be to assess whether your messaging addresses your meeting objective.
The distinction between a weak objective and a strong one matters more than most security professionals realise. A weak objective - "update the board on security" - gives you no anchor when the conversation drifts, and no measure of whether you succeeded. A strong objective is specific and outcome-oriented: for example, "gain board approval to increase the incident response budget following the Q3 breach trend across our sector." That objective shapes every slide you prepare, every metric you choose, and every question you anticipate. When a difficult question arrives, you can steer back to the objective rather than losing ground.
What Are the Three Key Questions Every Board Wants Answered on Cyber Risk?
Boards are not interested in technical detail on how the organisation has minimised risk. They are looking for insight on the state of the organisation's cyber security programme and the associated business risks. In each meeting, there are three key questions that need to be answered without getting bogged down in technical detail:
- What new or active threats are targeting organisations like ours?
- What did we do internally to reduce that risk?
- What is the current state of risk in our environment?
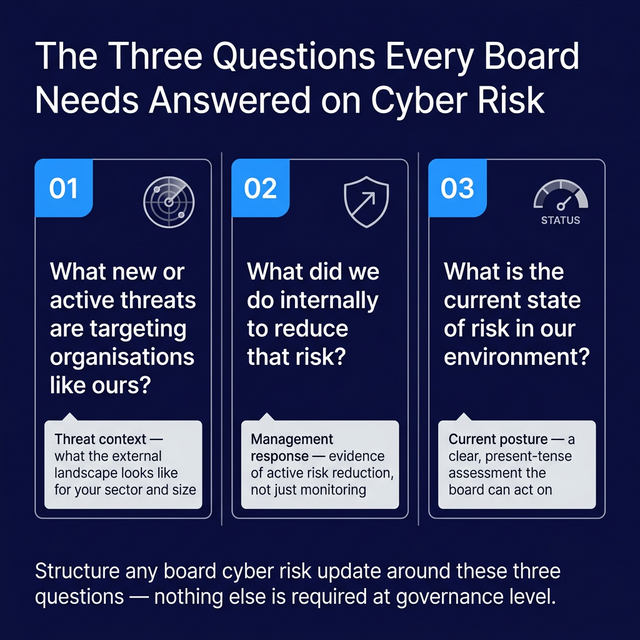
Those three questions form the structure of any effective cyber security board reporting update. They are also what distinguishes governance-level communication from a technical briefing. A board that gets clear answers to all three leaves the room equipped to exercise oversight. A board that gets a 47-slide deck of technical metrics leaves uncertain about all three.
The IBM Cost of a Data Breach Report 2023 found that organisations with a high level of board-level security oversight experienced breaches costing an average of USD 1.76 million less than organisations with low board oversight. That is not a security statistic - it is a governance and investment argument, expressed in the language boards respond to.
How Do You Understand a Board Audience Before Presenting Cyber Risk?
Understanding your audience is key in any situation. Building a relationship with board members can definitely help, but is not always possible as you may only see them every quarter. Conversations away from the formality of a board can allow you to understand their concerns and address them directly, what their responsibilities are, and ultimately understand the language and level at which to talk to them.
Before a presentation, a practical technique is to review board members' LinkedIn profiles and their Companies House filings. Understanding their professional backgrounds - whether they are chartered accountants, former operations directors, lawyers, or career non-executives - will tell you immediately whether they are likely to be more comfortable with financial risk framing, regulatory compliance language, or operational impact scenarios. This preparation takes thirty minutes and pays dividends in the room.
How Should You Translate Cyber Risk Into Language the Board Understands?
Board members are likely very smart people - if they were not, they would not be in their position (mostly). They may not be able to tell you the difference between EDR (Endpoint Detection and Response) and DLP (Data Loss Prevention), but they do not need to - it is not their job. Many board members, particularly in regulated sectors, will be more familiar with the language of risk registers, insurance exposure, and quantified financial loss than with technical security concepts. Use familiar frameworks and the board will understand, engage, and ultimately give you more effective support.
What happens when the translation fails
A CISO at a mid-sized UK professional services firm was presenting quarterly cyber risk updates. Board engagement was low: members were not asking questions, and approvals were being rubber-stamped without discussion. The CISO was reporting in technical metrics - patch compliance percentage, phishing click rates, vulnerability counts by severity. None of it landed.
After mapping each metric to a business outcome, the CISO switched to three board-level indicators: "Days to resolve our highest-priority vulnerabilities," "Estimated financial exposure from our top three risks," and "Status against our regulatory obligations." Board engagement increased noticeably. Questions shifted from absent to substantive. Within two review cycles, the board approved a budget uplift for incident response capability that had previously stalled.
The content of the risk position had not changed. The translation had.
Technical Language vs. Board Language
| Technical Term | What It Means to Security | Board-Level Equivalent | Example Board Question It Answers |
|---|---|---|---|
| Patch management / vulnerability remediation | Identifying software with known security flaws and applying vendor-issued fixes before attackers exploit them | How quickly we close the doors attackers could walk through - expressed as average days to remediate critical vulnerabilities, and percentage of systems current on patches | "If we were attacked tomorrow, how exposed are we to known weaknesses?" / "Are we meeting our insurance and regulatory obligations on security hygiene?" |
| EDR (Endpoint Detection and Response) | Software deployed on devices that monitors for malicious behaviour, detects threats in real time, and enables rapid containment | Our ability to detect and stop a threat on any device before it spreads - and our evidence that we can do so | "If an employee's laptop was compromised, how quickly would we know, and could we stop the damage before it reached customer data?" |
| Mean Time to Detect (MTTD) / Mean Time to Respond (MTTR) | Average time between an attacker entering the environment and the security team detecting them (MTTD); average time from detection to containment (MTTR) | How long an attacker could move freely through our systems before we stop them - directly linked to the financial scale of any breach | "In a worst-case scenario, how bad could it get before we act?" / "How does our response speed compare to industry benchmarks?" |
| Phishing simulation rate | The percentage of employees who click a simulated phishing link in internal awareness testing | The proportion of staff who could be socially engineered into giving an attacker an entry point - our human-layer risk exposure | "Are our people a significant risk factor? Is our training investment reducing that risk over time?" |
| Third-party risk / supply chain exposure | Cyber risks introduced through vendors, suppliers, and partners who have access to our systems or data | The security risk we inherit from every supplier relationship - including whether a supplier breach could become our breach, our liability, or our regulatory problem | "Are we exposed to cyber risk through our supply chain that we do not directly control?" / "Could a supplier incident trigger our own regulatory obligations?" |
Which Sources Do Boards Actually Consider Authoritative on Cyber Risk?
NCSC (National Cyber Security Centre), NIST (National Institute of Standards and Technology), CIS (Center for Internet Security), CREST (Council of Registered Ethical Security Testers), DoD (U.S. Department of Defense) - it is highly likely that while a security or risk professional considers these authoritative sources, the board may not. It is more likely the board has not encountered most of these organisations at all. When referencing authoritative sources to make a point, ensure the source is authoritative to the board, not to you. External audit and security assessment findings can be a good authoritative source.
There is, however, one NCSC resource that boards are increasingly likely to recognise. The NCSC publishes a dedicated NCSC Cyber Security Toolkit for Boards (Version 3.0, reviewed April 2025) specifically written for non-technical board members and senior leaders - not for security teams. It covers cyber risk appetite, board responsibilities for cyber oversight, and how to ask the right questions of your security function. It is now aligned with the UK government's Cyber Governance Code of Practice, giving it formal government backing. If you are going to reference the NCSC in a board meeting, this is the document to cite - because it is the one your board may actually have heard of, and the one that validates their role in governing cyber risk rather than delegating it entirely.
The WEF Global Cybersecurity Outlook 2025, published at Davos in January 2025, is another source boards recognise as authoritative. Its 2025 edition found that only 14% of organisations are confident they have the people and skills they need to manage their cyber security today, and that two out of three organisations report moderate-to-critical skills gaps. The World Economic Forum is an entity boards take seriously - citing its findings, alongside UK-specific data from the DSIT Cyber Security Breaches Survey, signals that you are operating at a level of strategic awareness appropriate to the room.
For any CISO framing cyber risk in a financial services context, it is also worth referencing NIST CSF 2.0 (published February 2024) as the current version of the framework - not "NIST" generically - and making clear how your programme maps to it. Boards and audit committees in regulated sectors are more likely to recognise a named, versioned framework than a generic acronym.
How Do You Bring New Board Members Up to Speed on Cyber Security?
With each meeting your board becomes more sophisticated - you relay more information and context, and the understanding of the organisation's security position matures. Board members come and go, and as a result there may be a requirement to bring new members to that same mature level. This works well if you can have conversations or dedicated sessions outside of and in advance of the board itself, thereby avoiding unexpected questions and getting the new member up to speed before they are in the room.
A practical mechanism is a brief written onboarding document - a two-to-three page board security primer that covers: the organisation's current risk posture, the framework you operate against, the three or four risks the board currently owns, and the decisions made in recent quarters. Sharing this before a new member's first meeting means their initial questions are better-formed, and the existing board's time is not spent re-establishing context.
Why Does Authenticity Matter When Presenting Cyber Risk to the Board?
Trust is built incrementally but lost quickly if authenticity is questioned. As the eyes and ears of the board in relation to their cyber risk, you need to be a trusted source. The number one rule in this regard is to never make anything up, even if you are under pressure to answer. Remember, it is perfectly acceptable to say "I'm not sure, but I will go away and find the answer." Fumbling around questions trying to work out an answer whilst in the spotlight is fooling nobody and people will see right through it. This takes us onto...
How Do You Prepare for Difficult Questions in a Cyber Risk Board Presentation?
It is not always going to be plain sailing - someone is going to ask you difficult questions and you need to be prepared for them. Anticipate difficult questions rather than hoping to avoid them. The best thing you can do is to anticipate the difficult questions and answer them in your update before anyone gets the chance to ask.
In your preparation, refer back to the minutes and actions from previous boards and avoid being caught out by having an action against your name which you have not progressed in the last three months (not talking from personal experience - definitely not). If you are preparing a CISO board presentation for the first time, read the minutes from the previous two or three meetings as a starting point for which questions are already live.
What Metrics Should You Present to the Board for Cyber Risk Oversight?
Avoid excessive metrics. Keep to 4-6 key indicators across three categories. No one is going to read them and even fewer are going to understand them. Try to condense your metrics to one or two pages and make sure they are meaningful. Reduce them to what the board needs to understand: is our situation getting better and are we moving in the right direction? What are the risks to the business?
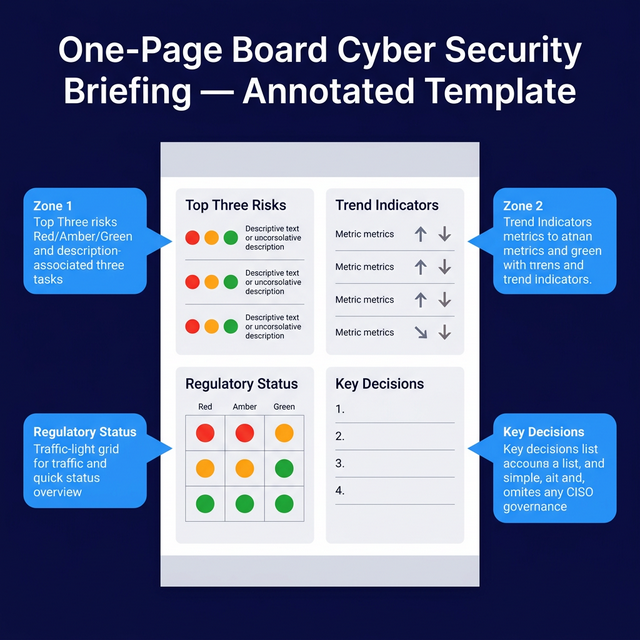
On the question of which metrics to include, a useful starting frame is three categories: posture (how well-protected are we?), response (how capable are we of responding?), and compliance (are we meeting our obligations?). Each category should have no more than one or two indicators. For posture, critical vulnerability remediation time and patch coverage are the most board-legible. For response, a plain-English description of incident response readiness is more useful than a raw MTTR figure. For compliance, a traffic-light status against your key regulatory obligations tells the board immediately whether there is a decision to make.
The WEF Global Cybersecurity Outlook 2025 found that only 14% of organisations are confident they have the people and skills they need to manage cyber security today - a talent and capability gap that makes board confidence in the security function more dependent on clear reporting, not less. If you are not giving the board a clear picture of your capability and direction, it is unlikely they are forming one elsewhere.
Taken Together: Context, Confidence, and Clarity
These ten principles align with board expectations: clear threat context, confidence in management, and transparency on state of risk. Context means helping them understand the threat environment in terms relevant to the business. Confidence means demonstrating that risk is being actively managed. Clarity means giving them the information they need to fulfil their governance obligations - and nothing they do not.
Get those three right, and your board presentation becomes a governance asset rather than a compliance obligation. If you would like support structuring your board-level security reporting, Precursor Security works with CISOs and security leaders across the UK - contact us to discuss your programme.
Frequently Asked Questions
What are the three questions every board should be asking about cyber risk?
The three questions that structure an effective board cyber risk update are: What new or active threats are targeting organisations like ours? What did we do internally to reduce that risk? And what is the current state of risk in our environment? These three questions cover threat context, management response, and current posture - giving the board everything they need to exercise governance without requiring technical knowledge.
What metrics should a CISO present to the board?
A board-level cyber security update should focus on three categories: posture (how well-protected are we?), response (how capable are we of responding to an incident?), and compliance (are we meeting our regulatory obligations?). Aim for one or two indicators per category at most - critical vulnerability remediation time, a plain-English readiness statement on incident response, and a traffic-light status against key regulatory obligations. Anything beyond this is for operational dashboards, not board papers.
Which sources do boards consider authoritative on cyber security?
Boards are less likely to recognise NCSC, NIST, or CREST as authoritative than a security professional would be. The exception is the NCSC Cyber Security Toolkit for Boards, which is specifically written for non-technical directors and is aligned with the UK government's Cyber Governance Code of Practice. External audit findings and assessments by recognised firms carry significant weight. The WEF Global Cybersecurity Outlook, IBM Cost of a Data Breach Report, and DSIT Cyber Security Breaches Survey are all sources boards are more likely to view as credible than standards body publications.
Why does authenticity matter so much in a board cyber risk presentation?
The board's ability to provide governance and oversight of cyber risk depends entirely on the quality of information they receive from the CISO. If you speculate, exaggerate, or obscure problems to protect your position, you undermine the governance function you are there to support - and once that trust is gone, it is extremely difficult to rebuild. The board does not expect you to have every answer; they do expect you to be honest when you do not.
How should you handle new board members who have no cyber security background?
Do not wait for a new member's first meeting to begin their education. A short written onboarding document - covering current risk posture, the framework the organisation operates against, the decisions made in recent quarters, and the three or four risks the board currently owns - shared in advance will bring them to a useful baseline. A brief one-to-one session before their first formal board meeting is even more effective, allowing them to ask questions they might not want to raise in a full board setting.
