What the UK Cyber Security and Resilience Bill means for your business
The UK Cyber Security and Resilience Bill updates the NIS Regulations 2018 to strengthen cyber security requirements for critical infrastructure operators, digital service providers, and managed service providers. The Bill introduces mandatory 24-hour incident reporting, penalties up to £17 million or 4% of global turnover, and new Secretary of State powers to intervene during active cyber threats. It is currently progressing through Parliament with implementation expected in 2026/2027.
What is the Cyber Security and Resilience Bill?
The Cyber Security and Resilience Bill is UK legislation designed to replace and expand the Network and Information Systems (NIS) Regulations 2018. The Bill addresses a threat environment that has changed substantially since the original NIS Regulations were transposed from the EU NIS Directive.
The UK now faces four nationally significant cyber attacks per week, according to the NCSC. That figure represents 204 significant incidents in the 12 months to August 2025, more than double the 89 recorded in the prior period. The 2025 UK Cyber Security Breaches Survey found that 43% of UK businesses experienced at least one cyber breach in the past year, with that figure rising to 74% for large organisations.
The Bill was introduced to Parliament in November 2025. It is currently in Committee Stage and is expected to receive Royal Assent and enter implementation in 2026 or 2027.
Why was the Cyber Security and Resilience Bill introduced?
Two incidents in 2024 exposed the gaps the Bill is designed to close: third-party supply chain compromise and inadequate incident reporting.
The Synnovis attack (June 2024). On 3 June 2024, the Qilin ransomware group attacked Synnovis, a pathology services provider for NHS trusts in south-east London. The attackers exfiltrated approximately 400GB of patient data, including NHS numbers, blood test results for HIV and cancer screening, and records from private healthcare providers. Blood testing capacity dropped to roughly 10% of normal. NHS England launched emergency donor appeals for O-negative and O-positive blood.
Over 11,000 outpatient and elective procedures were delayed. In the first 13 days, King's College Hospital and Guy's and St Thomas' trusts alone cancelled 1,134 operations and 2,194 outpatient appointments, including over 100 cancer treatments and 18 organ transplants. At least one patient death was linked to the disruption. Full recovery took until late autumn 2024. The financial cost to Synnovis was £32.7 million.
The MOD payroll breach (May 2024). A suspected state-sponsored attack targeted a third-party contractor managing the Armed Forces payroll network. The breach exposed personal data of up to 272,000 current and former military personnel, including names, bank details, and National Insurance numbers. The compromised system sat outside MOD's core networks. The contractor's security failures, not MOD's own defences, enabled the breach.
Both incidents share a common pattern: the attack vector was a third-party provider, not the organisation's own infrastructure. The Cyber Security and Resilience Bill directly addresses this by bringing managed service providers into regulatory scope for the first time.
Who is in scope for the Cyber Security and Resilience Bill?
The Bill regulates three categories of organisation, expanding well beyond the original NIS Regulations.
Operators of Essential Services (OES) include organisations in energy, transport, health, water, and digital infrastructure. These organisations were already regulated under NIS but face stricter duties under the Bill.
Responsible Digital Service Providers (RDSPs) cover online marketplaces, search engines, and cloud computing services. The Bill updates definitions to reflect how these services have evolved since 2018.
Regulated Managed Service Providers (RMSPs) represent the most significant expansion. MSPs and data centre operators are regulated for the first time. Any organisation providing managed IT, security, or infrastructure services to regulated entities now falls within scope.
The Bill also gives regulators the power to designate specific suppliers as "critical" to a regulated entity, bringing those suppliers directly under regulatory oversight regardless of their own classification.
The Bill has extraterritorial reach. Providers outside the UK that deliver services to UK-regulated entities may still fall within scope.
What are the incident reporting requirements?
The Bill introduces a two-stage incident reporting process with fixed deadlines, replacing the vague NIS requirement to report "without undue delay."
Stage 1: Initial notification within 24 hours. Regulated entities must notify their relevant regulator and the NCSC within 24 hours of detecting a reportable incident. This initial notification covers the basic facts: what happened, what systems are affected, and what immediate steps have been taken.
Stage 2: Full report within 72 hours. A detailed incident report must follow within 72 hours, covering root cause analysis, scope of impact, data affected, and remediation actions.
The Bill also expands what counts as a reportable incident. Under the NIS Regulations 2018, only incidents causing "significant disruption" to service triggered reporting. The CSRB adds incidents that compromise the "integrity or security" of a system, even if the service continues to operate. This includes attacker pre-positioning (establishing footholds for future attacks) and ransomware infections where data is exfiltrated but services are not yet disrupted.
After submitting the full report, regulated entities must also notify affected UK customers, detailing the nature of the incident and potential impacts.

How does the Cyber Security and Resilience Bill differ from NIS Regulations 2018?
The Bill is not a minor revision. It changes scope, reporting, penalties, and enforcement powers.
| Requirement | NIS Regulations 2018 | Cyber Security and Resilience Bill |
|---|---|---|
| Regulated entities | OES and digital service providers | OES, RDSPs, RMSPs, and data centre operators |
| MSP coverage | Not in scope | Directly regulated as RMSPs |
| Incident reporting timeline | "Without undue delay" (no fixed deadline) | 24-hour initial notification + 72-hour full report |
| Reportable incidents | Significant disruption to service | Disruption OR compromise to integrity/security (includes pre-positioning and ransomware) |
| Maximum penalty | £17 million (rarely enforced) | £17 million or 4% of global turnover (whichever is higher), potential escalation to 10% |
| Daily fines | Not specified | Up to £100,000 per day for ongoing non-compliance |
| Customer notification | Not required | Mandatory after full report submission |
| Supply chain powers | Limited | Regulators can designate "critical suppliers" and apply duties directly |
| Secretary of State powers | Limited | Emergency powers including network isolation directives |
| Alignment | EU NIS Directive (2016) | Informed by EU NIS2 Directive but UK-specific implementation |
What are the penalties for non-compliance?
The CSRB introduces a tiered penalty structure that mirrors the GDPR model.
Standard maximum: £10 million or 2% of global annual turnover, whichever is higher. This applies to breaches of general security duties and reporting requirements.
Higher maximum for serious breaches: £17 million or 4% of worldwide annual turnover, whichever is higher. This applies to severe or persistent non-compliance.
Potential escalation: The Bill includes provisions for penalties to rise to 10% of worldwide turnover in exceptional cases.
Daily fines: Up to £100,000 per day for ongoing non-compliance. This creates a strong financial incentive to resolve identified issues quickly rather than delaying remediation.
Regulators also gain expanded information-gathering powers. They can demand documents, commission audits, and issue binding directions to regulated entities.
What powers does the Secretary of State have?
The Bill grants the Secretary of State for Science, Innovation and Technology new emergency powers that did not exist under the NIS Regulations.
Designating critical suppliers. The Secretary of State can designate specific third-party suppliers as "critical" to regulated entities. Once designated, these suppliers must meet security duties directly, regardless of whether they would otherwise fall in scope.
Emergency directions. During active cyber threats, the Secretary of State can issue directions to regulated entities, including ordering network isolation or specific defensive measures. This power is intended for situations where a threat is systemic, affecting multiple regulated entities simultaneously.
Information sharing. The Bill strengthens the framework for sharing threat intelligence between the NCSC, regulators, and regulated entities. This includes a duty to report to the NCSC as the UK's Computer Security Incident Response Team (CSIRT).
These powers move the UK from the reactive posture of the NIS Regulations toward proactive, government-directed intervention during national cyber events.
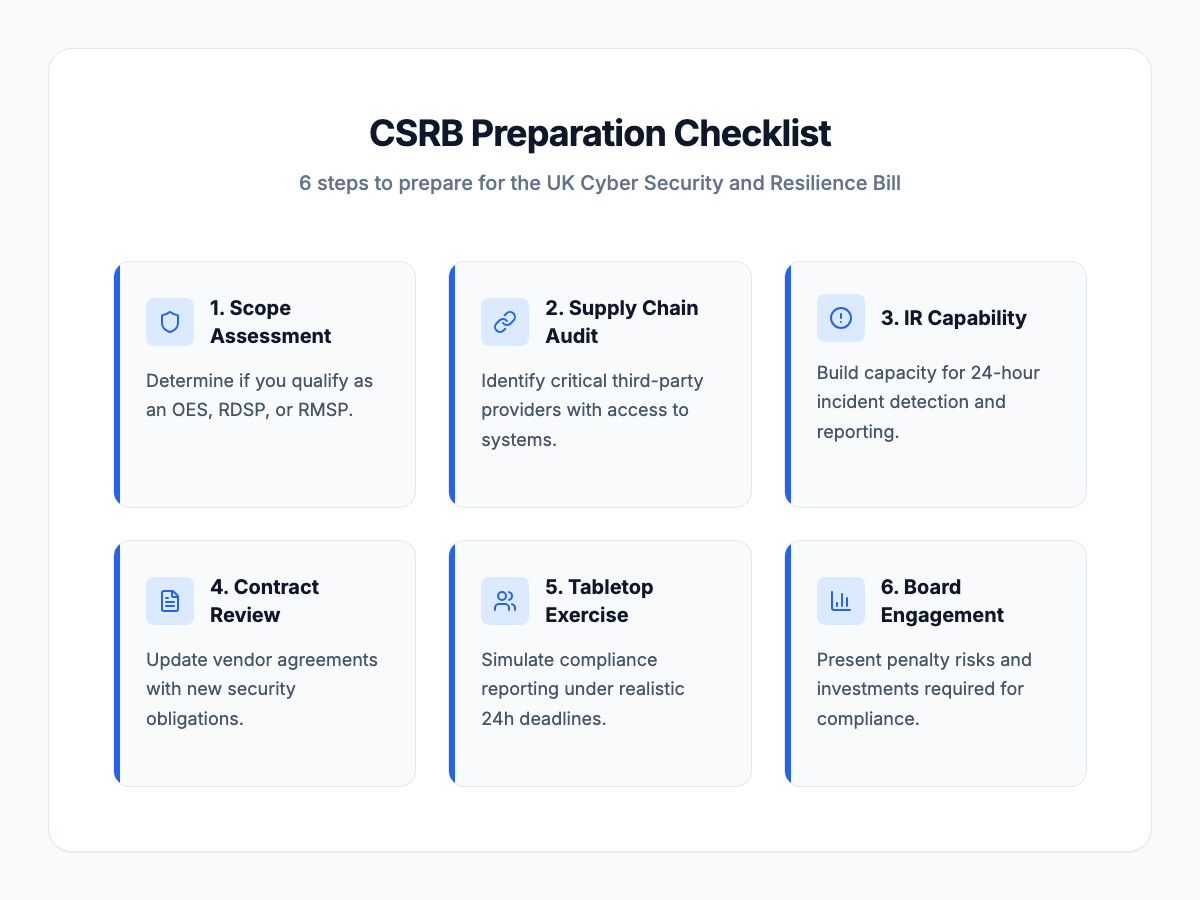
How should your organisation prepare for the Cyber Security and Resilience Bill?
Preparation does not require waiting for Royal Assent. The security capabilities the Bill mandates are the same capabilities that reduce breach impact.
1. Determine whether you are in scope. Map your organisation against the three regulated categories (OES, RDSP, RMSP). If you provide managed services, data centre hosting, or cloud infrastructure to regulated entities, you are likely in scope even if you were not regulated under NIS.
2. Audit your supply chain. Identify every third-party provider with access to your systems or data. The Synnovis and MOD breaches both originated from contractor weaknesses. Assess each supplier's security posture and contractual obligations. Consider whether any of your suppliers could be designated as "critical" under the Bill.
3. Build a 24-hour incident response capability. The 24-hour notification deadline requires organisations to detect, triage, and report incidents within one business day. This demands pre-built response processes, designated personnel with authority to act, and pre-drafted notification templates. If you cannot sustain this in-house, a managed detection and response (MDR) provider or incident response retainer should be in place before the Bill takes effect.
4. Review and update contracts. Vendor contracts should include security obligations, incident notification clauses aligned with the 24/72-hour reporting timeline, and audit rights. Existing contracts written for NIS compliance will need updating.
5. Conduct a tabletop exercise. Simulate a reportable incident, including the 24-hour notification process, 72-hour reporting, and customer communication. Test whether your team can meet the deadlines under realistic conditions.
6. Engage the board. The CSRB creates board-level accountability for cyber resilience. Present the penalty structure (£17M / 4% turnover), the supply chain risks evidenced by Synnovis and the MOD breach, and the investment required for compliance. Frame this as risk management, not an IT project.
What does the Cyber Security and Resilience Bill mean for managed service providers?
MSPs face the most significant change of any group under the CSRB. For the first time, managed service providers are directly regulated entities with their own security duties and reporting obligations.
As Regulated Managed Service Providers (RMSPs), MSPs must meet the same security standards as the organisations they serve. They must report incidents affecting their clients to the relevant regulator and the NCSC within 24 hours. They must notify affected customers after submitting a full report.
The insurance implications are immediate. Cyber insurance policies for MSPs will need to account for regulatory fines and the costs of meeting CSRB obligations. MSPs that cannot demonstrate compliance risk losing regulated clients who cannot afford the supply chain liability.
For organisations that rely on MSPs, the CSRB provides a new basis for vendor due diligence. Ask your MSP how they plan to meet RMSP obligations. Request evidence of their incident response capability, reporting processes, and security governance. If they cannot answer, that is a material risk to your own compliance.
Is the Cyber Security and Resilience Bill really a game-changer?
Some security practitioners view the Bill as evolutionary rather than revolutionary. It consolidates existing trends, building on CAF 4.0 evidence-based assurance, supply chain scrutiny, and incident response maturity, rather than introducing entirely new concepts.
That view has merit. Organisations with mature security programmes that already follow NCSC guidance, maintain tested incident response plans, and govern their supply chains will find the transition straightforward.
The difference is enforcement. The NIS Regulations had penalties on paper but rarely used them. The CSRB mirrors the GDPR penalty model, which has demonstrably increased board-level attention to data protection across UK and European organisations. Turnover-based fines, daily penalties for ongoing non-compliance, and Secretary of State emergency powers create accountability that the NIS Regulations lacked.
For mid-market organisations, the practical implication is clear. The security practices you should already have in place now carry regulatory weight. If your incident response process cannot meet a 24-hour notification deadline, or your supply chain oversight does not extend to MSP security, the CSRB turns those gaps from risks into regulatory exposures.
Frequently asked questions
When will the Cyber Security and Resilience Bill become law? The Bill was introduced to Parliament in November 2025 and is currently in Committee Stage. Royal Assent is expected in 2026, with implementation likely in 2026 or 2027. Exact dates have not been confirmed.
Does the Bill apply to my organisation if we are not critical infrastructure? If you provide managed IT services, cloud hosting, or data centre services to organisations that are classified as OES or RDSPs, you are likely in scope as an RMSP. The Bill's expanded definition of "in scope" entities captures organisations that were not regulated under NIS.
How does the CSRB compare to the EU NIS2 Directive? The CSRB is informed by NIS2 but is not a direct transposition. Post-Brexit, the UK is implementing its own framework. Key similarities include expanded scope, faster incident reporting, and higher penalties. Key differences include the Secretary of State's emergency powers and the specific designation of "critical suppliers."
What should we do first to prepare? Start by mapping whether your organisation falls within scope (OES, RDSP, or RMSP). Then audit your incident response capability against the 24-hour notification requirement. These two steps will determine the scale of preparation needed.
Will the Bill affect cyber insurance requirements? Yes. Insurers are likely to update policy requirements to reflect CSRB obligations, particularly for MSPs. Expect underwriters to ask about incident reporting processes, supply chain governance, and board-level cyber oversight.
